Facebook Cookie Stealing And Session Hijacking
Three days ago I finished the series on Gmail Session Hijacking and Cookie Stealing , due to a tremendous response of readers I planned to write a post on Facebook cookie stealing and Session hijacking. Facebook session hijacking can also be accomplished via a very popular tool called Firesheep(On a Wifi Network Only), which I won't be explaining here because I have already written it before in my post Facebook Hacking Made Easy With Firesheep
In this tutorial I will explain you how an attacker can capture your authentication cookies on a local area network and use them to hack your facebook account, Before reading this tutorial I would recommend you to part1, part2 and part 3 of my Gmail Session Hijacking and Cookie stealing series, So you could have better understanding of what I am doing here.
- Gmail Cookie Stealing And Session Hijacking Part 1
- Gmail Cookie Stealing And Session Hijacking Part 2
- Gmail Cookie Stealing And Session Hijacking Part 3
Facebook Authentication Cookies
The cookie which facebook uses to authenticate it's users is called "Datr", If an attacker can get hold of your authentication cookies, All he needs to do is to inject those cookies in his browser and he will gain access to your account. This is how a facebook authentication cookie looks like:Cookie: datr=1276721606-b7f94f977295759399293c5b0767618dc02111ede159a827030fc;
How To Steal Facebook Session Cookies And Hijack An Account?
An attacker can use variety of methods in order to steal your facebook authentication cookies depending upon the network he is on, If an attacker is on a hub based network he would just sniff traffic with any packet sniffer and gain access to victims account.
If an attacker is on a Switch based network he would use an ARP Poisoning request to capture authentication cookies, If an attacker is on a wireless network he just needs to use a simple tool called firesheep in order to capture authentication cookie and gain access to victims account.
In the example below I will be explaining how an attacker can capture your authentication cookies and hack your facebook account with wireshark.
Step 1 - First of all download wireshark from the official website and install it.
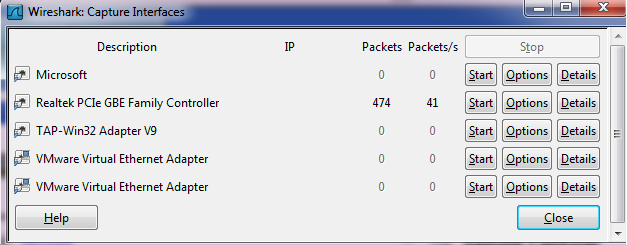
Step 2 - Next open up wireshark click on analyze and then click on interfaces.
Step 3 - Next choose the appropriate interface and click on start.
Step 4 - Continue sniffing for around 10 minutes.
Step 5 - After 10minutes stop the packet sniffing by going to the capture menu and clicking on Stop.
Step 6 - Next set the filter to http.cookie contains “datr” at top left, This filter will search for all the http cookies with the name datr, And datr as we know is the name of the facebook authentication cookie.
Step 7 - Next right click on it and goto Copy - Bytes - Printable Text only.
Step 8 - Next you’ll want to open up firefox. You’ll need both Greasemonkey and the cookieinjector script. Now open up Facebook.com and make sure that you are not logged in.
Step 9- Press Alt C to bring up the cookie injector, Simply paste in the cookie value into it.
Step 10 - Now refresh your page and viola you are logged in to the victims facebook account.
Note: This Attack will only work if victim is on a http:// connection and even on https:// if end to end encryption is not enabled.
Countermeasures
The best way to protect yourself against a session hijacking attack is to use https:// connection each and every time you login to your Facebook, Gmail, Hotmail or any other email account. As your cookies would be encrypted so even if an attacker manages to capture your session cookies he won't be able to do any thing with your cookies.









Omg, it really works, You have gained my respect dude, Can you tell me any other way to prevent cookie stealing else than https://?
ReplyDeleteIncognito-browsing.. Automatically prevents from cookie stealing
DeleteIn Chrome..
Ctrl+Shift+N - Incognito mode
In Internet Explorer
Ctrl+Shift+P - Inprivate mode
Good Luck,
aAnonymous
Nice Articles
ReplyDeleteAdmin of www.hackingarticles.in
Your "Cookie Injector" link is not working please give me a valid link.
ReplyDeleteYour "Cookie Injector" link is not working please give me a valid link.
ReplyDeleteOne of the best article.... great sharing
ReplyDeleteOne more thing that i want to add here is that ...if someone using https, so you can crack it too... http://www.ehacking.net/2011/06/crack-ssl-using-sslstrip-with.html
@George
ReplyDeleteYou can use a VPN solution too.
@Usama
Thanks for informing, I have updated the link.
Yes buddy, There are variety of methods you can use, You can even do it with cain and abel.
ReplyDeletehey rafay i hav read blog "how to install keylogger remotely on a computer " and i have olso try to do the same but i couldn't found ftp accounts and file manager to new directory ,can you please tell me where i shall found it.........
ReplyDeleteSo finally .. u posted how to bypass https encryption !!.. gud one man !!
ReplyDeletehey please tell me what to do after pasting the cookie value in cookie injector...
ReplyDeleteI wanna ask same question as Abreez one.
ReplyDeletecookieinjector script. link is not working . please adjust it
ReplyDeletegreat article!!!
ReplyDeletecan you please define a php script to capture cookie in your next article...
(http.cookie contains “datr”) was typed on filter then none data was found!!!!!!!! could you explain me???? I am surfing in a wireless network
ReplyDeletestep 3 and 6 are confusing---what do you mean by appropriate interface?
ReplyDeletehttp.cookie contains “datr”--not working
cookie injector not found for firefox
--please clarify above points--
@Anonymous 15
ReplyDeleteInstead of typing http.cookie contains "datr", just type http.cookie and search manually for the datr cookie.
i get an alert "All Cookies Have Been Written." Please Help Me
ReplyDelete@Sandhu
ReplyDeleteYes, you are getting the correct message, Just refresh your page and you will be inside victims account.
Rafay, does it works with the NVIDIA Force Networking Adapter... interface?
ReplyDeletei've done all the steps,but when i refresh the page nothing happen..please help me
ReplyDeleteHi, So I have made this facebook account for myself and logged in with it on my own PC and set up my information once. After a while I tried to log in again, but couldn't remember my password. unfortunately the password I used for my facebook account is the same as for my email, so I can't use the "forgot password" option. Having considered that I have used my own PC to log in, is there a way that login information is stored somewhere that I can retrieve them? (accessing cookies, etc) This is very vital for me as I have put some important information on that account without setting up proper privacy setting. Can you please help?
ReplyDeleteI can't seem to make it work.. :\ I have followed your instructions correctly and tried to hack myself for fun, but it didn't work.. I disabled the HTTPS browsing beforehand.
ReplyDeletehey , how would i know that after injecting the script , that it's the same account that i'm trying to hack ?
ReplyDeletei cant even find the “datr” thing manually too , Need help man plz .
ReplyDeletehow exactly it looks like ?
I am at step 8 and nothing. Please assist
ReplyDeletenikochi78@hotmail.com
after refreshing the page...nothing happens!! help please!
ReplyDeleteafter refreshing ...nothing happens why ?
ReplyDeletehow to hack gmail, if any one have dare to give 100% answer then send to my mail id : aabc8400@gmail.com
ReplyDeletefrom ur method it seems i have to know install those software in the victims computer and take is cookie id and then put in my comp and go in to his account.. right??
ReplyDeletewouldnt i be able to do all this in google chrome instead of using fire fox??
ReplyDeletewhat value should be given in 'cookie value'...
ReplyDeleterafay, u've got to response to this. I admit tht i'm only a script kiddie but you've got to tutor us on how this works. everything i did has been correct up to step 9. after the dialogue box pops out, telling tht the cookie's been written, nothing happens after i click on the refresh button. did i do anything wrong or has facebook upgraded their security system? i'd like to just see it work for once. please.
ReplyDelete@Oui
ReplyDeleteIt appears that you are getting the correct message, It should work, If it still does not work for you, I would need some information about your network.
First of all can you tell on what type of network are you on currently, Is it a wifi network?
Secondly are you on a hub based network or switched based network?.
It works perfectly....
ReplyDeleteI think the trick's not working because I'm capturing packets on a secured wireless network? Because I was using my college wireless network on my first attempt and all that was captured were my own data and on my second attempt, I am capturing on a neighborhood(3-4 houses sharing one wifi connection) wireless network where everybody's sick on facebook (they're seriously crazy in love with facebook, can't get off it when everyone's home - maybe a little bit of exaggeration but that's how I see it) but I can't find anything with 'http.cookie contains "datr"' neither with 'http.cookie' for anything regarding facebook? Can this work on a home or office wireless network where the network isn't public but anyone accessing it needs a passcode? I reckon it's still wifi though. I'm just itchin'.
ReplyDelete@Oui
ReplyDeleteIf you can't find the Http.cookie, it means that you haven't captured any of the facebook's traffic. There are wide variety of reasons why a session hijacking attack won't work, If you want to get a better understanding of session hijacking attacks, I would recommend read the three part series on Gmail session hijacking.
hey when I paste the cookie it says.........warning all cookies have been written........and then nothing happens........pls help
ReplyDeleteInteresting article you've got here. Well visit www.9jaboys.com for mobile and pc stuffs like free browsing tips. Free call, free sms....etc
ReplyDeletewireshark didnt capture any packets why plz help me
ReplyDeleteHow can you figure out the network you're on. Hub or switch base? Now that I'm lost
ReplyDeleteevery thing works except the facebook part, I can get the cookies and paste them into the cookie thing but it doesn't log me in. Please help! Im on an acer aspire 4011, verizon wifi hub.
ReplyDeleteeverything works but the last part when i regresh the facebook after putting all what you had said it does not login. it still onthe page of facebook login? what is going wrong?
ReplyDeleteeverything seems to work but the last part on facebook page.when i refresh the page nothing works could you please help!
ReplyDeletedoes the person need to be logged in from the same computer or network??
ReplyDelete@Rafay Baloch
ReplyDeleteU have 2 answer this one please!
Why does Wireshark only track the http.cookie of my ip address
only?!
I have managed all the steps, but when i open facebook and press "Alt" and "C" no cookie injector comes up. Why is this?
ReplyDeletewhat if we need to hack victim in WAN no in a LAN?? so the above procedure will still work?? or its failed to hack with WAN?
ReplyDeleteOkay, how do you Manually find the datr?
ReplyDeleteplease tell about WAN hacking facebook or yahoo or so on
ReplyDeleteis there any way to hack passwords with different networks that an attacker and victim use different network not in LAN ???
ReplyDeleteafter pasting the cookies in cookie injector then i reload the browser window,,,,nothing happen.why???????please clear the doubt
ReplyDeleteyoure cookie injector link is not working.. any other links that i can use?
ReplyDeletehey ... i pressed alt c but nothing happened :s what should i do !!
ReplyDeleteHi rafay plz give a attention here !!
ReplyDeletebro , :) ... http.cookie contains "datr" This one is wrong !
plz Update this post .. the correct one is http.cookie contains datr
without quotes " " .. :) hope u understand ..
and the second mistake is -- " Step 2 - Next open up wireshark click on analyze and then click on interfaces. "
It should be open Capture ! then click on interfaces . :)
and yeah my problem plz bro give a solution to this ..
i downloaded and installed wireshark and when i clcik on capture then interface then i get an error like this -- " There are no interfaces on which a capture can be done. "
plz tell me how to solve this problem ?
Hope u reply soon bro ....
by d way...........if facebook is used with HTTPS .........thn how can u hack tht id with cookies..bcoz cookies gets expires.........lolz......d best way is keylogger hiding under jpg.
ReplyDelete@Anonymous 55
ReplyDeleteHTTPS hasn't anything to do with the cookie expiring process, It makes sure that the information passed through the form is encrypted and both the parties can have a secure communication, Facebook does it well in expiring the cookies, but not much when encrypting the cookie.
Hey Rafay, r you frm Pakistan??
ReplyDeleteI want to hack the facebook account of someone who unfriend me. Is there a possible way to do that since where not living together? I also can't locate the facebook id number. The only display i got is something like www.facebook.com/xxxxxref=ts. Any reponse will be appreciated. Thankyou.
ReplyDeletehey does this stuff work on a wired internet connection?
ReplyDeletehey i tried this i got the message "All Cookies Have Been Written." i refreshed the page...now how to enter into victim's profile ? i typed victim's profile link in the search bar but it wasn't of any use..!
ReplyDeletebrother u gotta answer this one....
ReplyDeletehow can we b sure that thats the same account we want to hack in.....???
-ash
its not doing nothing after i refresh it after last step?! please help
ReplyDeleteI got to the pasting the cookie in the box, and it told me "all cookies have been written." How do I fix this? Please respond as soon as possible (anyone), I need to get into this account before tomorrow night!!
ReplyDeleteHey it take me to my own account dude.how i'll get someone Authentication cookie?? plz reply soon
ReplyDeleteWill wireshark work on wifi interface atheros adapter? And Im a bit confused, will it only hack peopel who are using the same network or someone using a deifferent network?
ReplyDeleterafay please i have no idea of facebook hacking, as someone used my pics in a wrong manner although i send directly by myself. will you please let me know how i can hack the account in order to save myself.
ReplyDeletewell i have no much idea about facebook and hacking so keeping in view these points so i can do efficently.
dude u should help us......
ReplyDeletemany of us are having same problem .....
nothing happens after refreshing ....what can be the cause...???
@All those who are not getting into the account after refreshing the page, Here are the possible reasons:
ReplyDelete1. You are probably sniffing https:// traffic, which means that the cookie is encrypted.
2. You are probably sniffing on a hub based network.
Where I need to paste the script, in Greasemonkey?
ReplyDeleteplizz can u hack dis account n most probably close it...facebook account : mfahim@xtra.co.nz
ReplyDeleteplizz..he's harrassin me n sayin bad things to me..plizzz
Dear Rafa,
ReplyDeleteI wanna know my wife's facebook password.She logged in using my laptop 15 days ago. Now she is not here. How can I get the password information from that? Please help me
Sadi
I think, for this u need physical access to the victim's Computer .
ReplyDeleteI still cant understand it, If someone is on a wire connection [internet] then how to hack his account??
ReplyDeletenice..
ReplyDeletehey guyzz visit my blog at
www.almashackingtutorials.blogspot.com
What am I doing wrong, when every time I try to insert the code, a window pops up, telling me ''All Cookies Have Been Written'' ?
ReplyDeletethanks for answering
great share
ReplyDeletePress Alt C to bring up the cookie injector, Simply paste in the cookie value into it. i don't get it
ReplyDeletebro wire shark isn;t capturing any data on my pc. plz help :)
ReplyDeleteHey it works.
ReplyDeleteitz opening my own facebook account only...not of the victim dude...
ReplyDeletehey itz showin my own facebook account ..not of the victims ya
ReplyDelete@Shiya
ReplyDeleteIt means that you have captured your own cookies instead of the victims.
Hiya rafay, I've downloaded wireshark but when I click analyse in the tool bar, interface isn't an option. Any idea?
Deletein step 6 how we will know thhat the cookie is of datr
ReplyDelete(http.cookie contains “datr”) was typed on filter then none data was found!!!!!!!! could you explain me????
ReplyDelete(http.cookie contains “datr”) was typed on filter then none data was found!!!!!!!! could you explain me????
ReplyDeleteden how can i capture victims cookie ?
ReplyDeleteden hw can i capture victims cookie ?
ReplyDeleteden hw can i capture victims cookie dude ?
ReplyDeleteive tried and still cant do it... i know my ex is cheatin on me, but this time i think its with someone i think of as a friends... im tryin to gain his password to his facebook :'( and ive had no success... anyone willing to help me im desperate :(( contact me by my email brandy_b787@yahoo.com
ReplyDeletei downloaded greasemonkey and cookieinjector scrip, but when i run cookieinjector script i said it is from unknow publisher and wont work :(: here is what i got :line 21
ReplyDeletechar: 2
Error : "unsafewindow" is undefined
Code: 800A1391
Source: microsoft JScript runtime error
hope u find me a solution mr. rafay
byt thanks for ur aarticles.
A message appears saying that "all cookies have been written"then I refreshed the page but nothing happend.Please help me
ReplyDeletei took my own facebook cookie i log ou then i logged in still same result when i log out the session dies ?
ReplyDeletei tried to inject only the datr it doenst work ?? i tried to extract it doesn also work !!! should i preporm MITM before ?
how to capture victims cookies? i try many times but still stucked at there..
ReplyDeleteother than this,
is it cannot use wifi?
I have tried all the steps but i can never get the correct cookie, while I wait the 5-10 minutes do i have to do anything on facebook to actually get the correct cookie?
ReplyDeletehello rafay i am a fan of yours since i read your work and i was wondering if you could help me out someone hacked my friends (girlfriends) account and i wanted to hack it to get it back but there is a problem apparently the person who hacked her facebook also hack her hotmail so she cant reset the password i tried to use your method but it didnt work so now i wanted to see if you could help me hack her account or what you suggest my email is t_cangri@hotmail.com thx for the help
ReplyDeletehello rafay i am a fan of yours since i read your work and i was wondering if you could help me out someone hacked my friends (girlfriends) account and i wanted to hack it to get it back but there is a problem apparently the person who hacked her facebook also hack her hotmail so she cant reset the password i tried to use your method but it didnt work so now i wanted to see if you could help me hack her account or what you suggest my email is t_cangri@hotmail.com thx for the help
ReplyDeleteWhy can I only capture the cookies on my computer but not other people's computer when they share a same wifi network with me?
ReplyDeletehey can you tell me how to hack a retro hotel??? a retro hotel is like habbo.co whit many online accounts :) the retro hotels names is :dibbo.dk :) hope you can help me ??
ReplyDeleteI have followed the all procedure stated above. But when i press the ALT+c Nothing happens. Any solution. . .
ReplyDeleteafter i refresh,,i still couldnt go to victim's account. I am sure that it is HTTP. so, what am i supposed to do rafa??
ReplyDeletethanks
J
i cant found interfaces after clicking 0n ANLAYZE...what can i d0?
ReplyDeletehttp.cookie "dart" can be found....what do i d0?
ReplyDeleteI can only say SUPERB
ReplyDeleteFirst of all, this must be a good program...Now i do not want to use profanity but i am sick of all of you here who are trying to get something that does not belong to you. You would not like it if this was done to you. I am a victim on a similer scale on facebook but a very intence one. Here is a change for some of you to do good in life. HELP ME PLZ. I play poker on Facebook and my chips keep on getting stolen over and over again. I have changed my password and login multiple time, installed a new version of windows, bought a new security software, added addon to my browser but still same thing. I get hacked the same day that zynga give me my chips back. They are tracking my issue on a daily basis but its been a while either its multiple people stealing from me or just one. Who ever it is , he or she is good. my wireless is secure, atleast i think so. I use mac filtering and changed the admin password and login as well. dont know what else to do...can someone tell me what can i do...thanks plz reply to aamir_f_khan@yahoo.com
ReplyDeleterafy bro can u help me out bro i have got the cookies but tell me how to put them ?
ReplyDeletei have added Greasemonkey and the cookieinjector is just a script
plz tell me how to use it ?
and where i will fine this wireshak cookie dump ?
bro plz plz plz reply soon
when i click on interfaces in wireshark, it says "There are no interfaces on which a capture can be done." Please Help
ReplyDeletehi .. I can not always get it to work when I log on to facebook so I have only been opened my own account sometimes .. What should you do if you want to open someone else's account we mail or ID number .. I want to hack a specific account because the person behind the account hetzer people and illegal sites etc.. I really hope you will help. You may want. send me an email to facebookteam093@gmail.com
ReplyDeletehi .. I can not always get it to work when I log on to facebook so I have only been opened my own account sometimes .. What should you do if you want to open someone else's account we mail or ID number .. I want to hack a specific account because the person behind the account hetzer people and illegal sites etc.. I really hope you will help. You may want. send me an email to facebookteam093@gmail.com
ReplyDeleteSo does it work if the victim is using a different computer but using the same wifi?????
ReplyDeleteWhat can I do to solve the hub issue? Do I need to buy switch or is there another way?
ReplyDeleteis nok work please help
ReplyDeleteHey this work today because i find the datr cookie and inject but when reload the web appear facebook to login or open my facebook
ReplyDeleteAlt +C not working
ReplyDeletei mean cookkie injector is not working
ReplyDeleteNo offence and I don't want to promote it, but could someone tell me if hijacking/hacking facebook is possible? I came across a posting at google groups, there is a guy who can actually get you password of your enemies. Funny, hah!
ReplyDeleteIf there is any one around here with some good knowledge, do share it out here. For the reference, here is group url: http://groups.google.com/group/pay-to-click/browse_thread/thread/1cab446b734697c7
You dont need wireshack to do this you can go to google chrome inspect element--> resources-->local storage. Also i think this doesnt work bcause facebook got https
ReplyDeletehi want to hack facebook account please help me
ReplyDeleteDear brother, I have tried to hack facebook account using this trick but yet i am unable to perform it. I successfully steel the cookies using wireshark and inject them but when i refresh the page, nothing happens. plz brother help me plzzzzzzzzz
ReplyDeletehow can i choose a victim?
ReplyDeletehow to know im hacking whose account and how to choose victim?
ReplyDeletehey this happens only when both r on same netwrk rite...
ReplyDeletei am getting the sane login page after refreshing.... how to do i am not understanding.. please help me
ReplyDeletehey i am not understanding what are u saying... ia m getting the same login page after refreshing....... how to do it...please help me...
ReplyDeletecant capture packets using wireshar..help me please..
ReplyDeletecant capture cookies by using wire shark..bcos i'm using Huwai usb nodem...if u can help me pls...
ReplyDeleteIf I can have access to another computer's cookie directory, is there any way to extract the datr file and use it, or it has to be online to hack the account? I am searching my own cookie directory, but i use chrome and i am not sure that I have found the right datr format. I used SQLite Manager to extract the cookie directory for chrome, and I import the results in the Greasemonkey but nothing seems to happen.
ReplyDeleteIf you could tell what I am doing wrong it would be very helpfull.
Thanks in advance
If I can have access to another computer's cookie directory, is there any way to extract the datr file and use it, or it has to be online to hack the account? I am searching my own cookie directory, but i use chrome and i am not sure that I have found the right datr format. I used SQLite Manager to extract the cookie directory for chrome, and I import the results in the Greasemonkey but nothing seems to happen.
ReplyDeleteIf you could tell what I am doing wrong it would be very helpfull.
Thanks in advance
I am Able to copy cookie of my own account and gaining access to mah account ........ but how can i find cookies of another people account on the same wi-fi connection ?????? i m getting cookies of my own account only on wireshark ................my gmail is
ReplyDeletetochetanwadhwa@gmail.com
sir ......... will u plzz tell me that how to select interface on a wi-fi network in wireshark to get coookies of another's gmail accounts active on same wi-fi network ???
ReplyDeleteCookie Injerctor dont pop up.
ReplyDeleteThe following display filter isn't a valid display filter:
ReplyDeletehttp.cookie contains “datr”
Help ??
The following display filter isn't a valid display filter:
ReplyDeletehttp.cookie contains “datr”
help
It goes to my own facebook page. how do i get the victims cookies?
ReplyDeleteGuys to those who do not see any result after pressing ALT + C , please follow this :
ReplyDelete1-Go to Tools (press alt if you are using last firefox version)
2-go to Greasemonkey > Greasemonkey-options
3-then press " Add " and write the website you have cookie for NOTE:(exept Gmail & google ) and make sure the website followed by " * " expmle : http://www.facebook.com/*
4- then click at Ok
and open http://www.facebook.com/ (without the " * " ; make sure you are not logged in.
5-and press ALT + C , and past the cookie you have copied from wireshark , (at the copying step , at the details of the packet you captured look for " Cookie : " and right click at the cookie line and Copy>Bytes>printable only.
6-Now refresh the facebook page ( F5 )
Congratulations you are done.
it is working 100% perfect thanks rafay
ReplyDeleteto those people who said that it doesnot work
you have to log to the facebook account and donot logout because when you logout the cookies ends and you could do that from internet explorer browser and use the cookies on the firefox by alt+c and paste then refresh while opening the account from another explorer without logging out
guys if the password had changes from other pc this can work??
ReplyDeleteplzzz answer
This capturing way just succeed packets between your own local computer and server/website that you visit not whole network or specific IP address
ReplyDeletehey when i use wireshark and click on start it says no packet capture..??why plzz help
ReplyDeletehow can i capture interfaces if i am using wireless as my internet connection ( it's like an internet using a flash drive)
ReplyDeletethankxxx... i needed it badly.
ReplyDeleteIt s not working....After i do everything...my filter directs me to a result...something like....ajax/chat/buddy......(something like that)...i copy it as Directed...n inject it...after getting the message cookies have been written....i refresh n i dont get anything....the same login page gets reloaded again!!!....i am using broadband...PPoE....n at some on a single connection...on single computer!!...and whats that...End to end encryption?
ReplyDeletecan u tell me, what is useful to capture packets on a 3g usb connection
ReplyDeletePlease, tell me how can i get a cookie from any friends browser
ReplyDeleteand i tried this but it is not working!
Please, tell me how do i get cookie from friends browser?? And i tried this , but it is not working!! when i set a cookie into cookieinjector after that automatically redirect into google and this process remain continue!
ReplyDeleteHey after refreshing nothing happens.......what to do.....
ReplyDeleteFirst, thank you for this and for the answers that you give to us ;)
ReplyDeleteThen, I need u're help, Everything work until the "refresh moment", when I refresh, nothing happens, and I'm french so I did'nt really understand what you said before :/ so could you explain for me what's the problem, knowin that I'm (on/in) wifi, and the account i'm tryin to hack, is (in/on) https, so what can I do ? Thanks for all again, bye.
after downloading and installing wireshark, when im opening it its coming The procedure entry point DecodePointer could not be loacted in the dynamic link library KERNEL32.dll. What to do?? Please help!
ReplyDeleteIF our victim is online on FB from cell, will this work?
ReplyDeleteI've gotten everything down except once I copy and paste the code and then refresh the screen, nothing happens... HELP!
ReplyDeletehttp.cookie contains datr doesnt work it has syntax error pls help
ReplyDeleteturkog@itu.edu.tr mail me
http.cookie contains datr doesnt work it has syntax error pls help me turkog@itu.edu.tr mail me pls
ReplyDeleteDoes this work on a remote computer? for example I want to hack and account but the person is logging in from Argentina.
ReplyDeleteThanks :)
If I have access to a person's cookies on a shared computer, can I just take the cookie .txt file from their user appdata folder and get the value that way? If so, how do I get the value once I have the .txt file?
ReplyDeleteBut how i access to a exact victim's account?
ReplyDeleteThis only works on your network.. Argentina won't work.. To set up wireshark you have to choose your interface first but selecting either wlan0 for wifi of something like eth0 for wired.. If not then wiresshsark doesn't know where to capture from. You can set that up right in the menu. After choosing an interface hit start capture and follow the instructions for session stealing. And if you want the exact account then steal the exact cookie for his account.
ReplyDeleteGood Article.I'll try this and reply again,
ReplyDeletehey firesheep is not working on firefox 14.0.1
ReplyDeletehow to know who are you hacking????
ReplyDeletedid it work on datastick ?/////////////////?????????????????????????????????
ReplyDeleten which browsser???????????
now...I cant get it to work..Doesnt do anything when i refresh,,any more detailed descriptions on what to do?
ReplyDeleteNow..What do i do when i get in there, when i refresh it does nothing. How do you control it...Any more specific instructions?
ReplyDeletei get this error "All Cookies Have Been Written" then i refresh the page but not working.... plz help
ReplyDeletei get some msg as you reply to:Sandhu
ReplyDeleteYes, you are getting the correct message, Just refresh your page and you will be inside victims account.
but its not working.... plz reply...
I followed the steps, but ended up with the same problem as most of the people: when refreshing, nothing happens. Could it be becauze i am using a hub based network ? It s a computer, not a laptop.
ReplyDeleteI followed the steps and ended up with nothing happening after the refresh. I am using a hub based network. What seems to be the problem ? :/
ReplyDeletePlease help...
ReplyDeleteIn Step 7, you say to "right click on it and goto Copy - Bytes - Printable Text only."
ReplyDeleteWhat, exactly, is "it"? Where would I find it? Help please? Thanks.
how to hack fb using above method, if a person is on hub network...
ReplyDeleteit really works man.....i logged on to my account and stole my own cookie through Wireshack and i successfully logeed in...
ReplyDeleteAdmin u deserve my respect man.......
what to do with cookieinjector script
ReplyDeletei could not able to bring up the cookieinjector with alt+c, is there any other way to bring that up ?
ReplyDeletehow do i identify the information that i found is the one who im going to hack?
ReplyDeleteFacebook nolonger http, now cookie cant sniff through https:// ssl protected website... need to use other method to disable ssl/https and sniff to http://
ReplyDeleteError on opening the cookie injector ... how to fix it sir.?
ReplyDeletetnx
This is useless! it isn't working :@
ReplyDeleteI need your help please i did every thing 1 by 1 but i start interfaces i never find any datr files
ReplyDeleteif you wanna prevent the session stealing please sure that you are not in a hub environment. Well yes we can still sniff by ARP pois. in a switch environment, just in order to make it harder to do it. You may use things like HMAC to sign the variables for the web server and browser to check it by codes like:
ReplyDelete----------------------------------------------------------------
< F'k(m) > < C >
HMAC(ve,k)= hash --------> user -------> server
|
|
< HMAC(ve,k) > V
if hash == HMAC(moded(ve),k) <----------- compute
else print {error};
[drop session]
-----------------------------------------------------------------
When i clicked on interfaces it said I've got none... so now what.
ReplyDeleteHey listen, I did everything you said and it all went normal, but when i pasted the cookie in that text box, i get a message saying "all cookies have been written" and then i hit enter. the n as you said i refresh the page but ABSOLUTELY NOTHING HAPPENS. and yes the victim was logged in during that time. Please help me man. thanks.
ReplyDeleteguys pls help ctrl-c not working!!
ReplyDeleteSomeone Should so hack someone for me... This isnt my comp so i cant just DL things to it. <3
ReplyDeleteWould this method work if the victim is on a different network entirely?
ReplyDeleteHow can I find the victims cookie, there is a lot of these things(I'm a newbie)
ReplyDeleteWhen I paste the printable text in wireshark cookies dump on facebook login page it says "All cookies have been written' plz tell me what to do
ReplyDeletePlease answer me whether I need access to victim's pc for this method to work?
ReplyDeleteMy question is IF our victim is online on FB from cell, will this work? how to hack wifi password on android Waiting For Your Answer!
ReplyDeletedoes this still work on 2015 ? xD
ReplyDeleteHttp.cookie containing datr is not there in filter
ReplyDeleteOnly Http.Cookie_pair. Is there
What to do now
Http.cookie containing datr is not there
ReplyDeleteRather Http.Cookie_pair is showing in the filter
How shall I do now
I enter in filter http.cookie contains “datr” but there is not show anythink plzzz help
ReplyDeleteDear sir and Friends ,
ReplyDeleteWe can hack the facebook account by using inspect element also.......
By using inspect element we can visible the victims password by our naked eye
ReplyDeletenice one bro How to Hacking articles
ReplyDeleteAfter i click on analyze, interfaces is not showing !!
ReplyDeleteWhat can i do ???